OpenAI gives your teams the power to build production-grade agents. Obsidian ensures security scales with them.
Unlike off-the-shelf AI tools, OpenAI's API lets developers build and deploy custom agents and applications with full control over models, prompts, and integrations.
Orchestrate multi-step tasks like customer support triage, data enrichment, document processing, and internal tooling, powered by custom agents built directly on OpenAI models.
Use OpenAI to write and review code, generate documentation, and build internal tools faster — so engineering teams spend less time on repetitive tasks and more time shipping.
Give developers and product teams the flexibility to build purpose-built AI applications without waiting on third-party vendors or prebuilt solutions.
Unmonitored OpenAI agents silently spread risk across every application they access and every data connection they make.
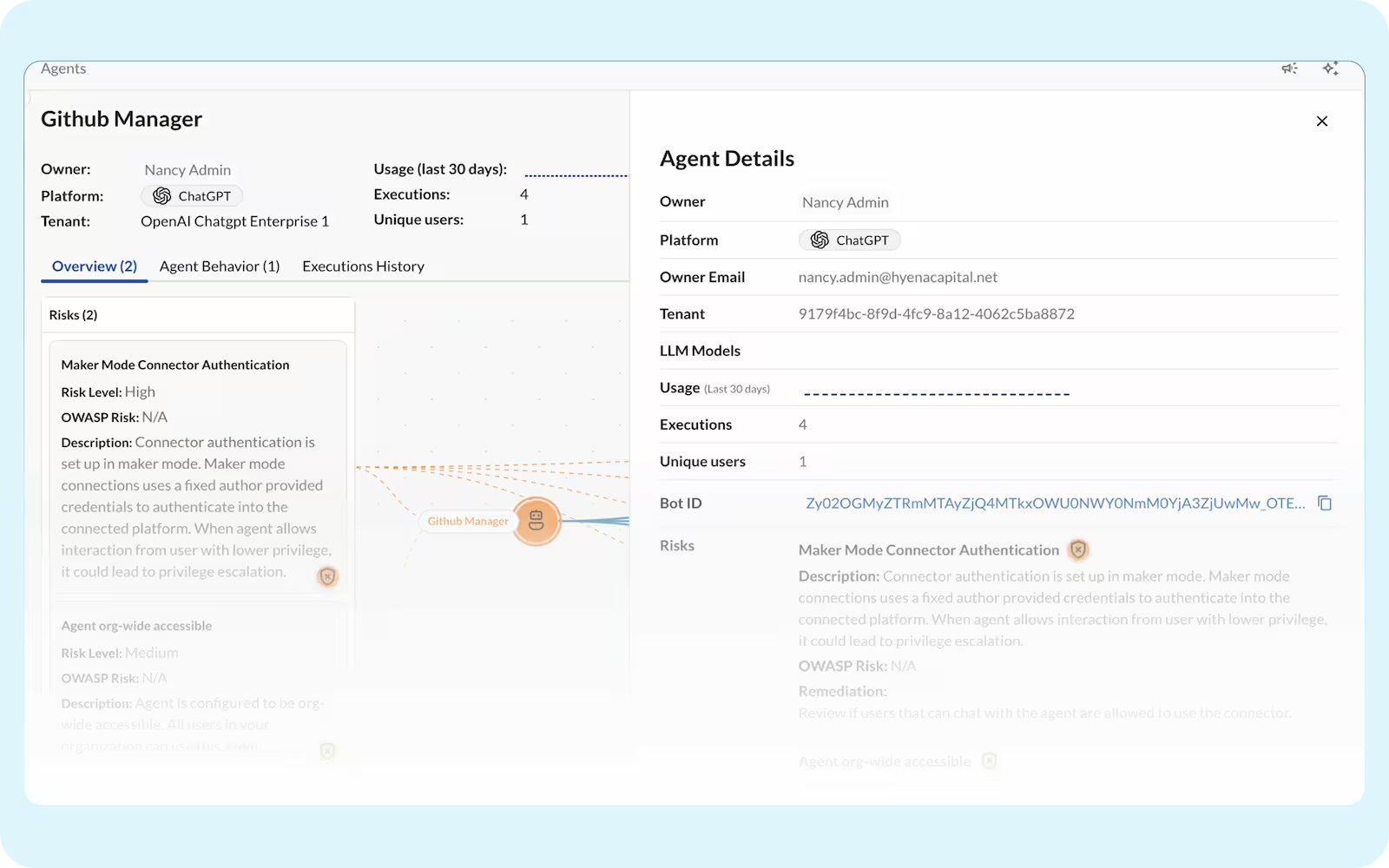
OpenAI agents can inherit admin-level rights or unnecessary access, giving them far broader reach into your data than any single user should have.
Agents can operate with greater rights than the users who built them, accessing and acting on data they were never explicitly authorized to touch.
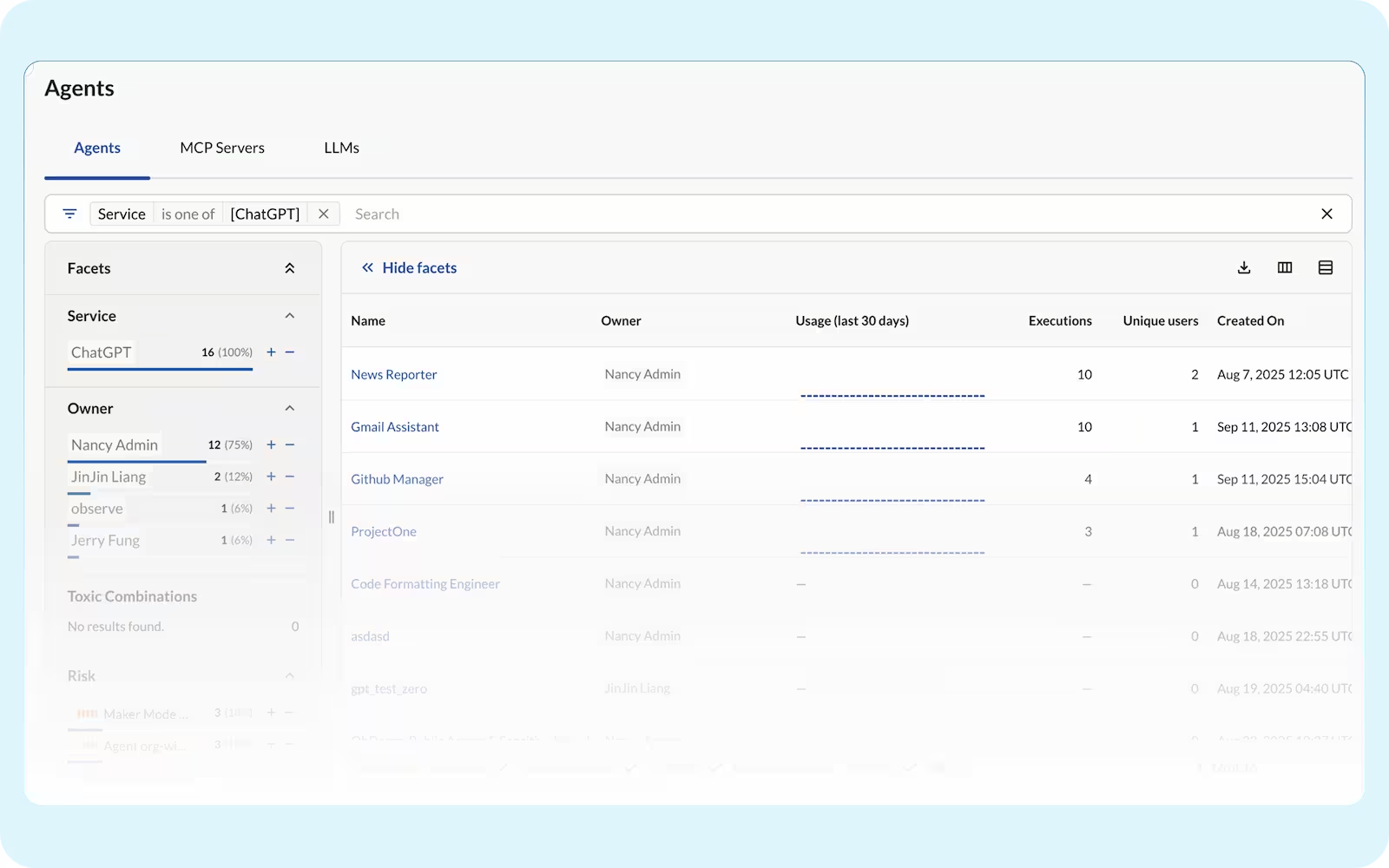
Business teams can build and deploy OpenAI agents without security review, leaving unknown agents operating across your SaaS environment without guardrails.
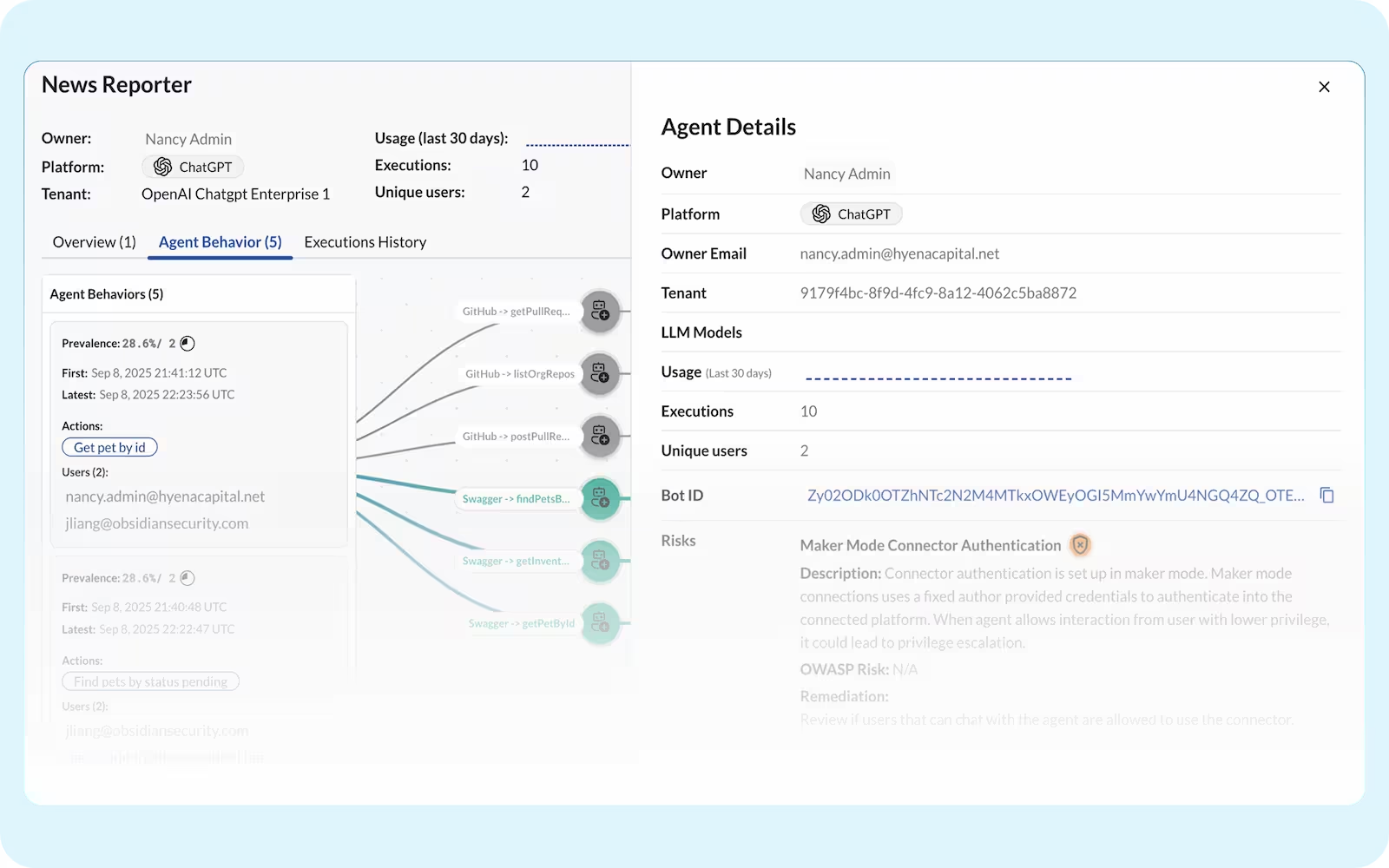
Over-permissioned or misconfigured agents can exfiltrate sensitive data across connected applications faster than traditional security tools can detect.
OpenAI gives developers the tools to build powerful agents, but visibility into what those agents access, invoke, and expose is left entirely to you.
No single view of which agents, MCP servers, and models are running across your tenants.
Native logs weren't built to capture risky tool calls and cross-service actions, especially from agents running outside OpenAI on platforms like Claude.
Agent permissions are scattered across every app they touch. Without a unified view, you can't know your true exposure until something goes wrong.
Agents act on behalf of users but aren't always bound by the same limits. Without a full identity graph, you won't know when an agent quietly exceeds the access its user was granted.
Map, monitor, and manage your agents with a single governance layer.