

Scale AI with confidence knowing every agent, its owner, connected tools, models, and MCP servers are automatically discovered, mapped, and assessed the moment they appear.
Agents ship faster than manual reviews can keep up. Inventories go stale, executions are missed, and blind spots grow. By the time you review one platform, dozens more agents are already running elsewhere.
See and secure every user interaction with AI, from chatbots and in-app features to low/no-code and developer-built systems.
.avif)
.avif)

Out-of-the-box integrations with all major agent platforms, so you can get full visibility and governance within hours.
Start securing AI agents on day one with out-of-the-box visibility, governance, and runtime protection. Then pair agent data with additional application context to surface and stop risks that neither source reveals alone.
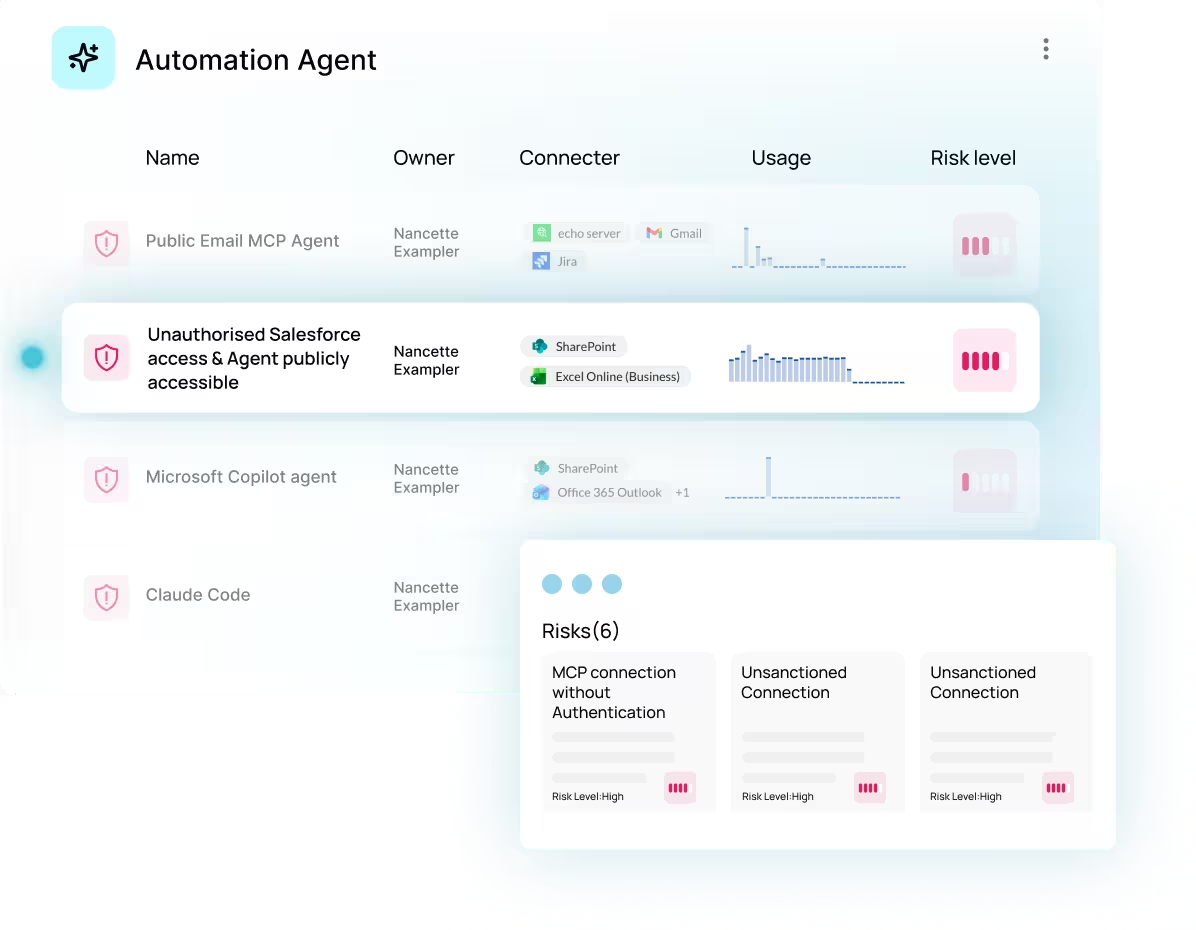
Obsidian automatically discovers agents in real time across business platforms, including low-code tools and AI platforms. It also captures agent creation events through the browser in popular SaaS apps, so visibility does not depend on manual tracking.
Each agent is mapped to its owner, platform, applications, connected tools, models, MCP servers, and permissions. This creates a live inventory that stays current as agents appear.
Every discovered agent is instantly assessed against OWASP-aligned risk factors and best practices. That helps surface issues such as hardcoded creator credentials and prioritize them by severity.
Yes. Shadow agents and orphaned agents are common problems, and Obsidian maps each agent to an owner and its connections so these gaps are easier to spot.
Support across platforms includes Vertex, Foundry, Bedrock, ChatGPT, and Claude, plus low-code environments like Agentforce, Microsoft Copilot, and n8n.
Correlating agent data with SaaS and identity context helps uncover risks that agent data alone may miss. Examples include detecting sensitive data access across apps, identifying posture issues behind agent risk, and enforcing guardrails against actions like privilege escalation through action chaining.