Claude Code gives developers powerful autonomous capabilities. Obsidian gives security the visibility and controls to govern them.
Claude Code lets developers move faster: writing, reviewing, and refactoring code autonomously. But every agent operating in your dev environment needs governance to match its capabilities.
Developers use Claude Code for autonomous coding workflows, cutting time spent on repetitive engineering tasks and speeding up delivery cycles.
Orchestrate multi-step tasks like PR reviews, test generation, dependency updates, and infrastructure changes without manual handoffs between tools or teams.
Let engineers delegate routine work to Claude Code agents such as debugging, documentation, and code search, so they can focus on higher-complexity problems.
Claude Code agents operate inside your development environment with broad permissions: read/write access to repositories, pipelines, and infrastructure. Without visibility, one misconfiguration or unexpected action can have production-level impact.
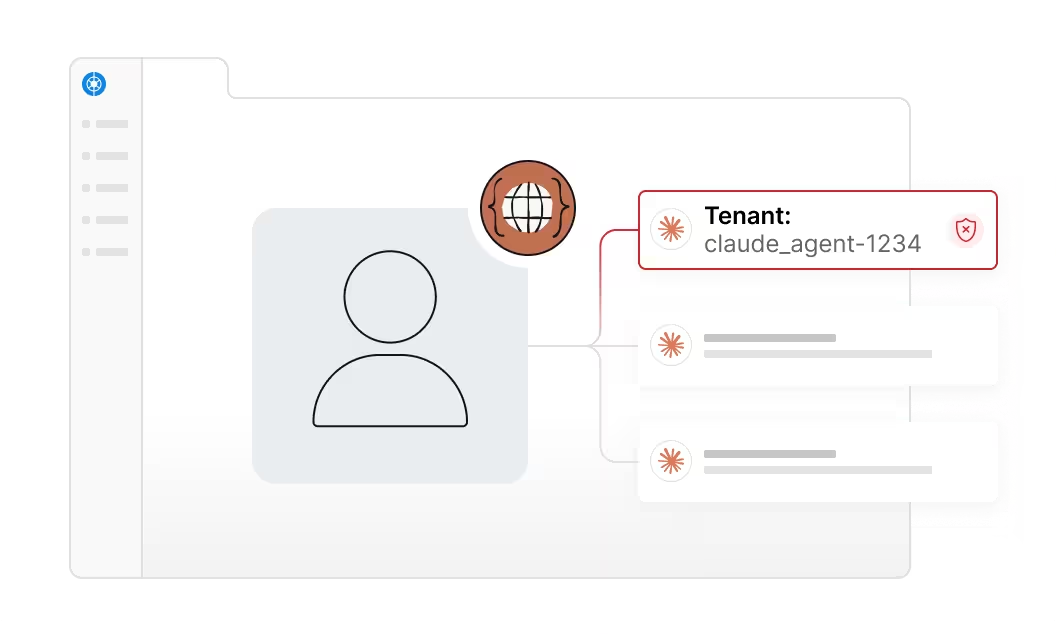
Claude Code agents inherit the credentials and permissions of the developer who configured them, often with access to repositories, CI/CD pipelines, and cloud infrastructure that far exceeds what any single workflow requires.
Developers can spin up Claude Code agents locally or in shared environments without security visibility into what tools they're invoking, what systems they're touching, or what MCP servers they've connected.
Claude Code agents execute autonomously, interacting with connected systems without a human in the loop. Without runtime controls, there's no way to catch a high-risk action before it completes.
Claude Code agents invoke MCP-connected tools to interact with backend systems. Without visibility into those tool calls, security teams can't see what's being accessed, modified, or exfiltrated downstream.
Claude Code's native controls weren't built for enterprise security. They don't surface the tool calls, MCP connections, and cross-system actions that security teams need to govern a developer agent.
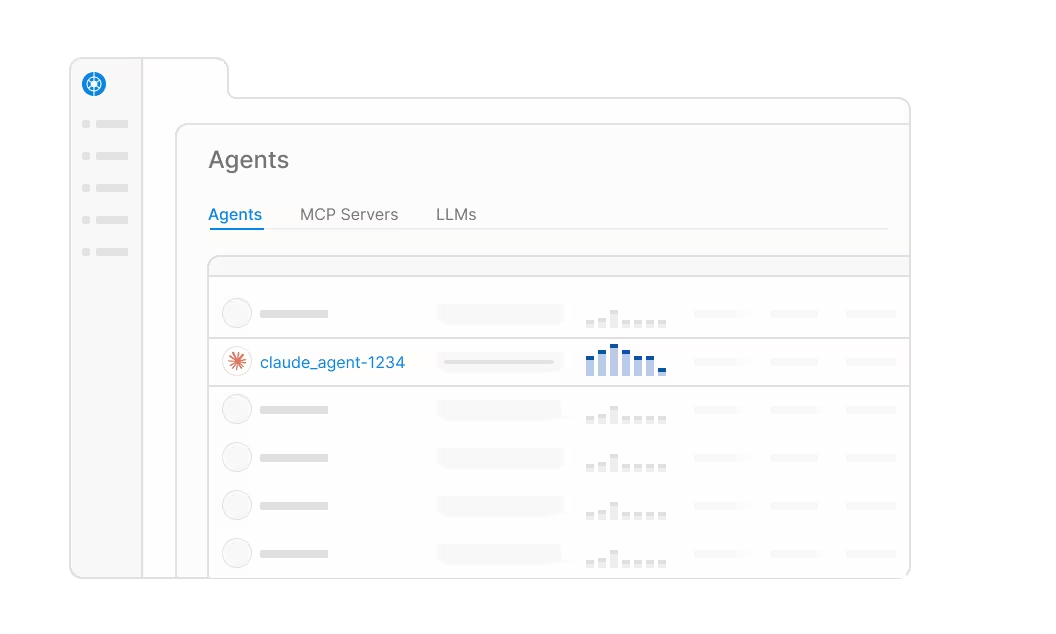
Claude Code agents are deployed across engineering teams without a central record of what exists, who owns each one, what MCP servers it's connected to, or what it's executed on.
Anthropic's logs capture model interactions but weren't designed to track tool calls, MCP invocations, or what happens downstream when Claude Code executes inside your development stack.
Claude Code agents accumulate permissions across every repository, pipeline, and system they touch. Without a unified view of effective access, blast radius is unknown until something breaks.
Claude Code agents invoke MCP servers to interact with backend systems and services. Without visibility into those connections, unsanctioned MCP usage and downstream risk go completely undetected.
Map, monitor, and manage your agents with a single governance layer. Sign up today to get a demo of our Claude Code capabilities.