n8n puts powerful automation in anyone's hands. Obsidian makes sure security keeps pace.
Unlike off-the-shelf automation tools, n8n lets technical teams build and deploy custom AI agents and workflows across any app, API, or data source — with full control over logic, infrastructure, and integrations.
Orchestrate multi-step tasks like data pipeline management, API integrations, incident routing, and cross-tool synchronization across your entire stack.
Use agents to connect tools, trigger actions, and automate handoffs between systems, cutting the manual work out of your engineering and ops workflows.
Let technical and ops teams build custom automations without relying on dedicated engineering resources, using n8n's flexible, code-optional builder.
Every n8n agent inherits user permissions and operates across your SaaS and AI environment Without visibility into what they're doing, risky actions and data access go undetected until it's too late.
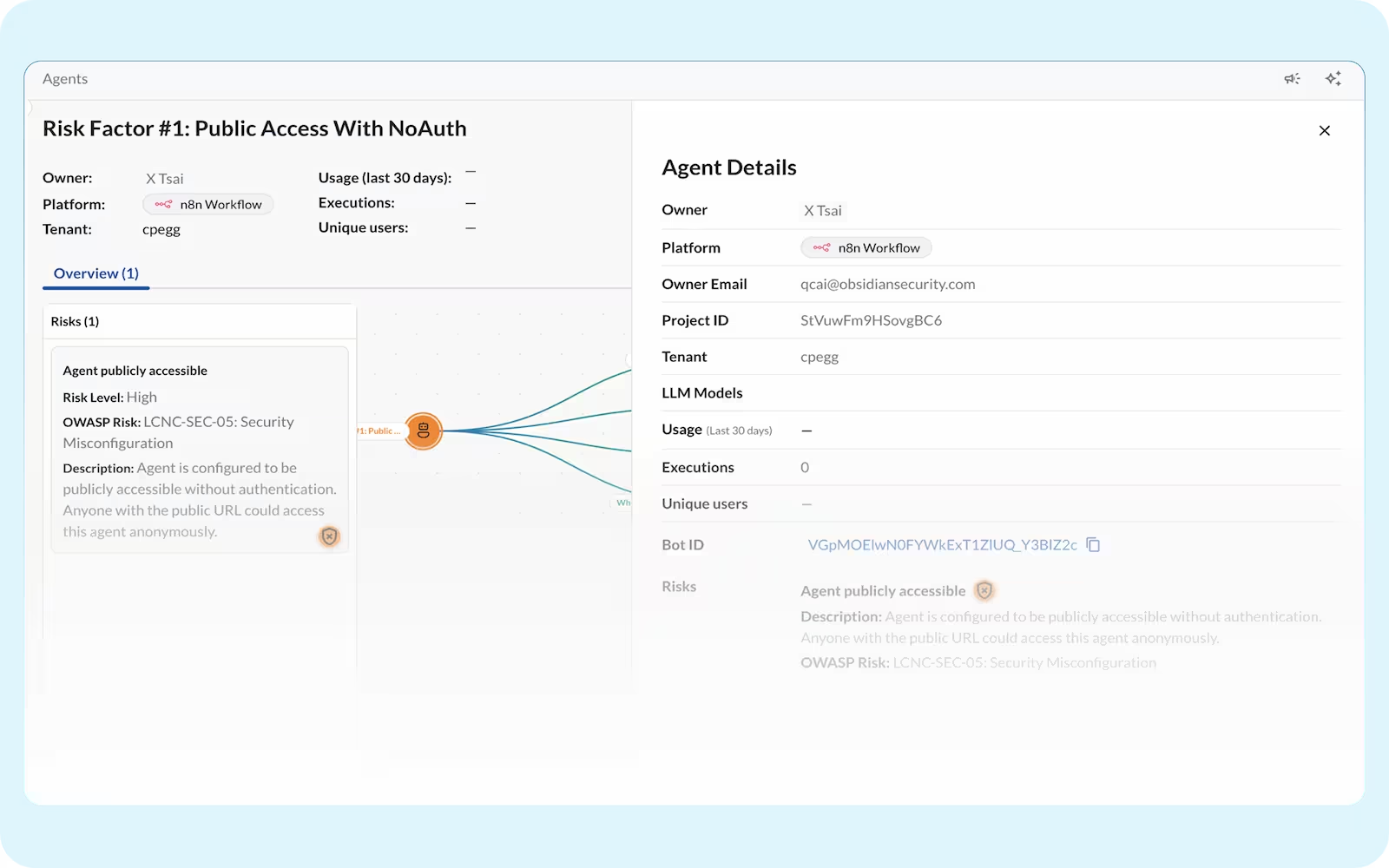
n8n agents often request broad access (like read/write all data) when only narrow permissions are needed, creating unnecessary exposure.
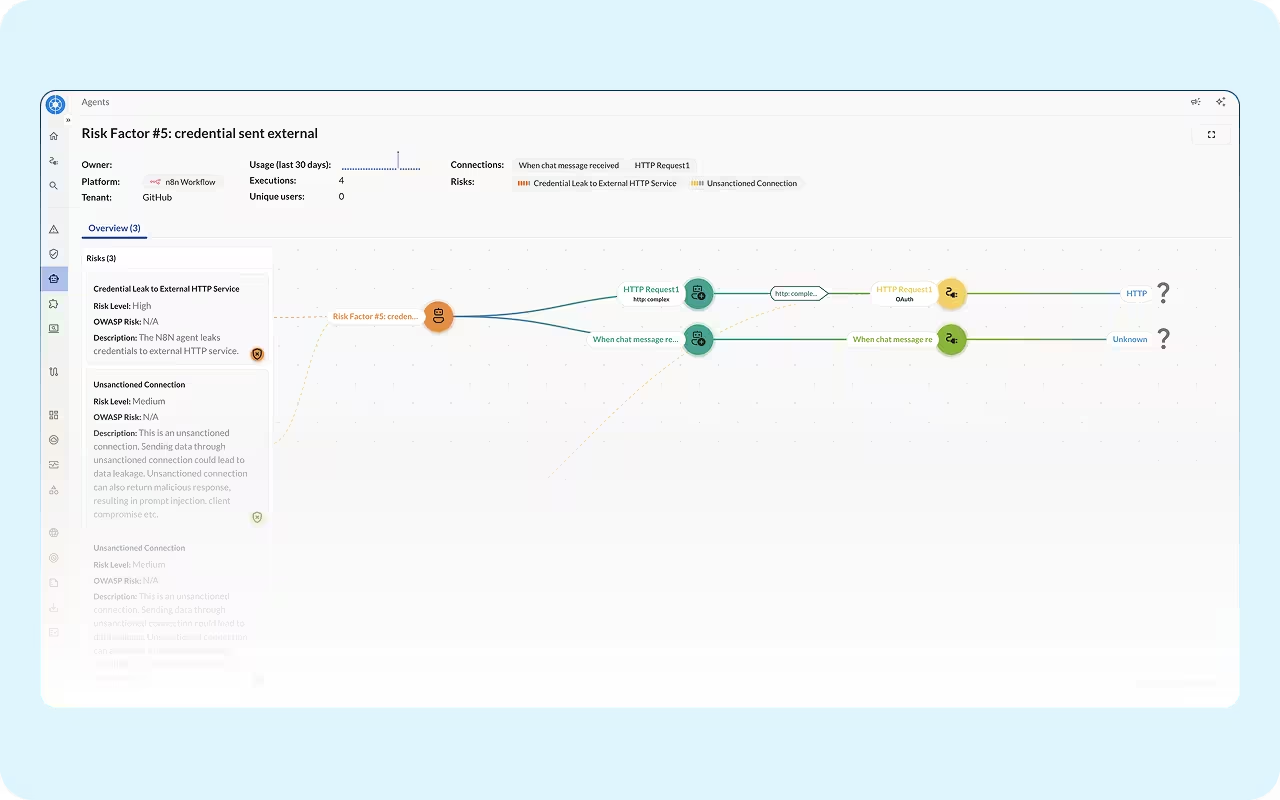
A single node connecting to core SaaS like Salesforce or Google Drive can become a hidden entry point.
Automated flows can accidentally sync sensitive customer or employee data across systems.
Workflows built outside security’s view make it impossible to enforce policies and monitor agents.
Community nodes or third-party plugins may contain vulnerabilities or malicious code that slip into production workflows.
N8n surfaces your agents but can’t show you every risk, leaving security teams blind to unauthorized tool calls, excessive permissions, and unsanctioned cross-service actions.
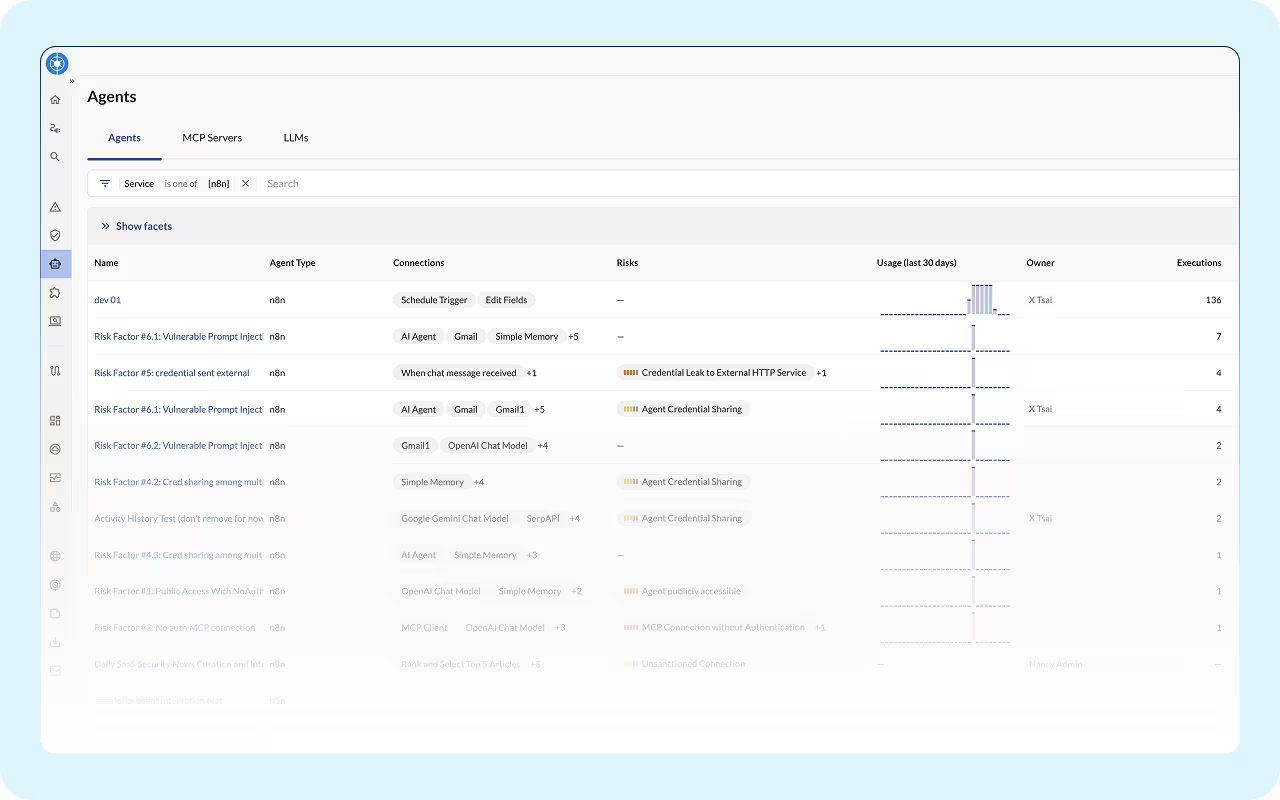
No single view of which agents, MCP servers, and models are running across your tenants.
Native logs weren't built to capture risky tool calls and cross-service actions, especially from agents running outside n8n on platforms like Claude.
Agent permissions are scattered across every app they touch. Without a unified view, you can't know your true exposure until something goes wrong.
Agents act on behalf of users but aren't always bound by the same limits. Without a full identity graph, you won't know when an agent quietly exceeds the access its user was granted.
Map, monitor, and manage your agents with a single governance layer.