Ensure every Bedrock agent has the right security controls in place without slowing down your users.

Unlike prebuilt AI assistants, Bedrock lets users quickly build and deploy agents with custom AI models designed for the task at hand.
Orchestrate multi‑step tasks like ticket triage, infra changes, CRM updates, and HR workflows.
Use agents to write and review code, streamline processes, and improve customer experience.
Let non‑developers build workflows and agents without waiting on central engineering.
Amazon Bedrock lets teams deploy agents that invoke AWS services and act on behalf of users, but without the right visibility or controls, risky permissions and data access can become security incidents.
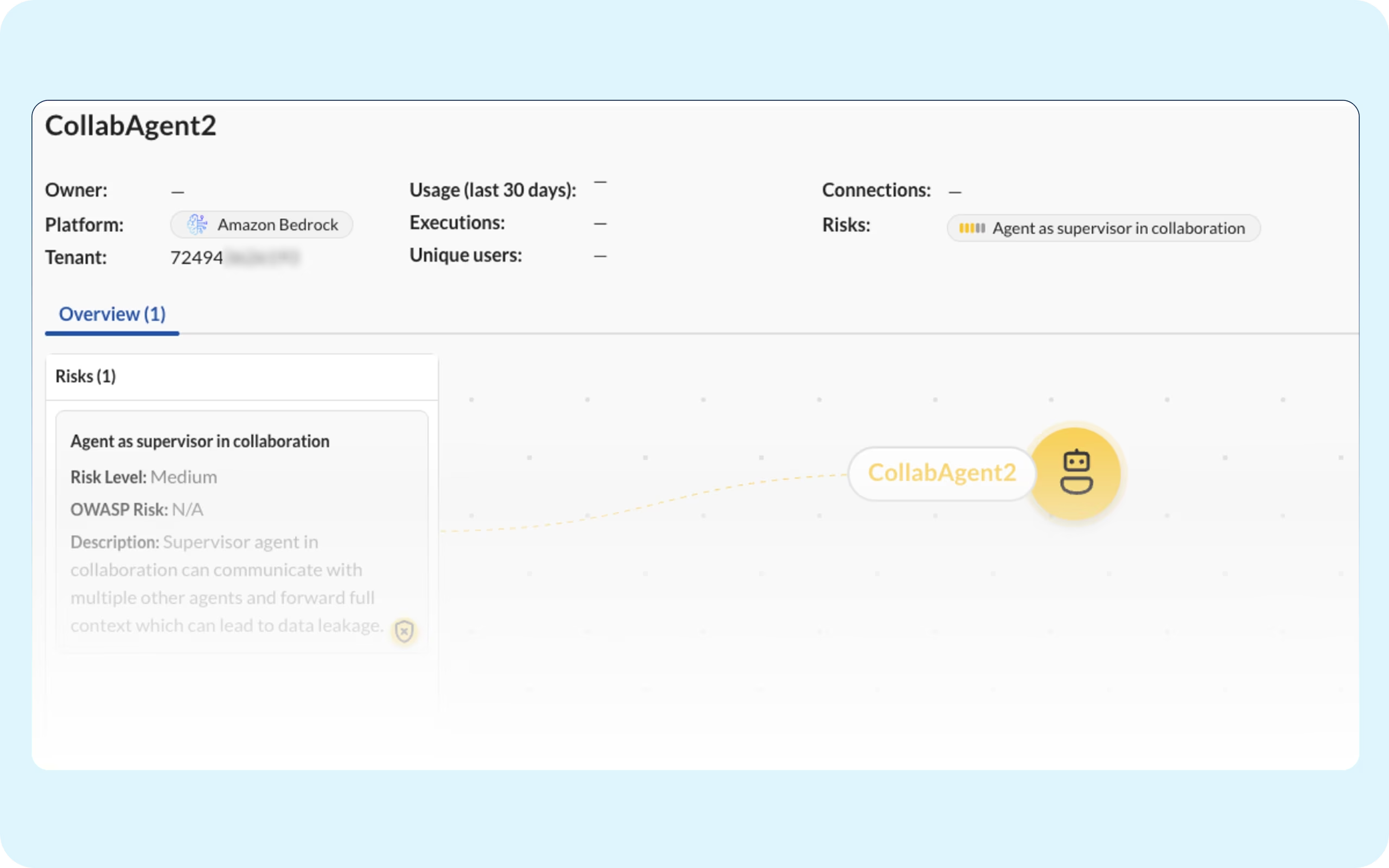
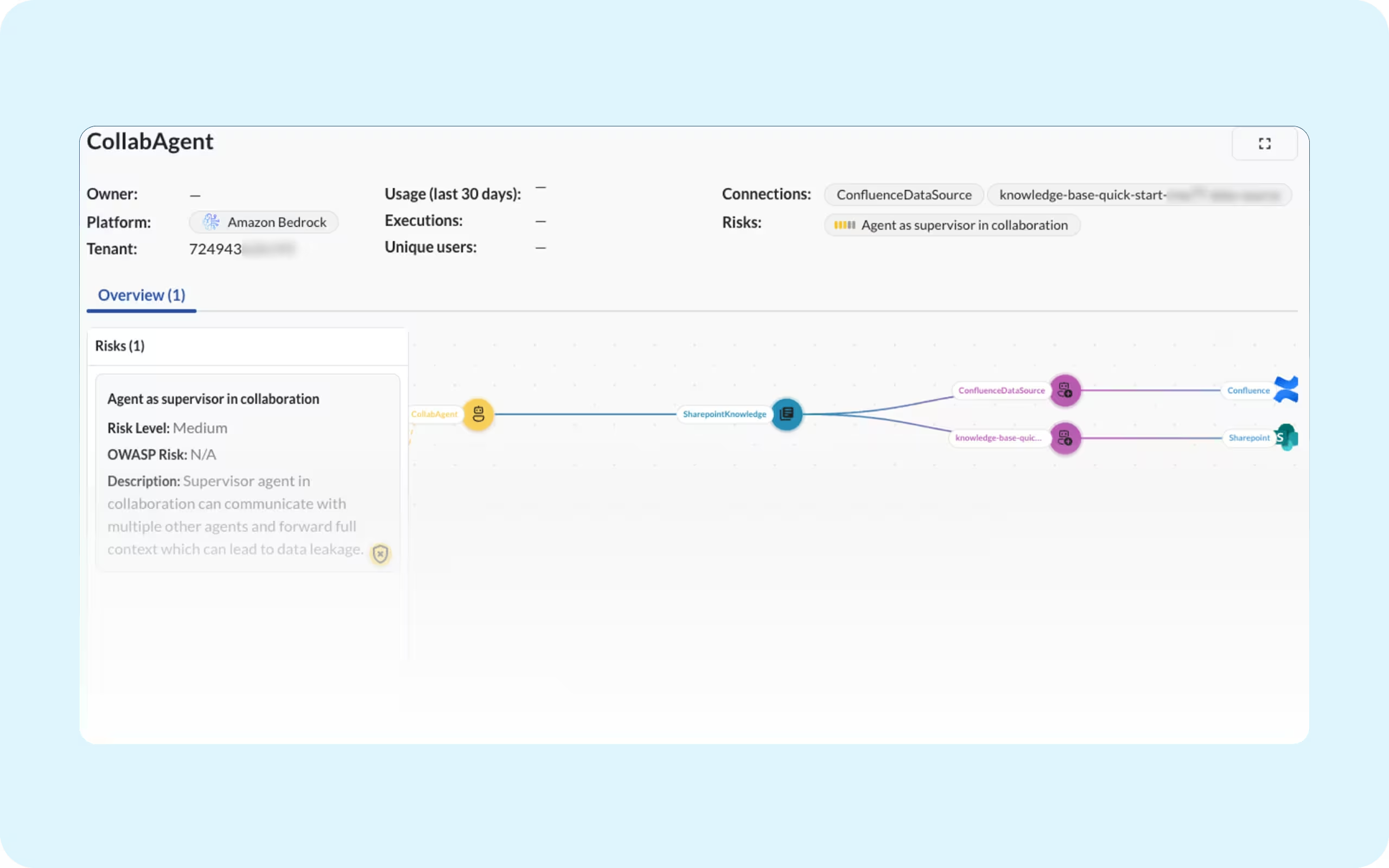
An over‑permissioned HR or finance agent can query classified internal knowledge across your enterprise applications.
Bedrock-connected agents can change or delete source code, pipelines, or IaC in GitHub/Cloud Build, turning one misconfiguration into rapid, production-impacting damage.
Business teams can expose CRM or ticket data as agents autonomously generate and share content externally.
Similar agent use cases can run in Vertex, Copilot, and Bedrock; without unified governance, fragmented policies and logs hide risky cross‑platform behavior.
Amazon surfaces your agents but can’t show you every risk, leaving security teams blind to unauthorized tool calls, excessive permissions, and unsanctioned cross-service actions.
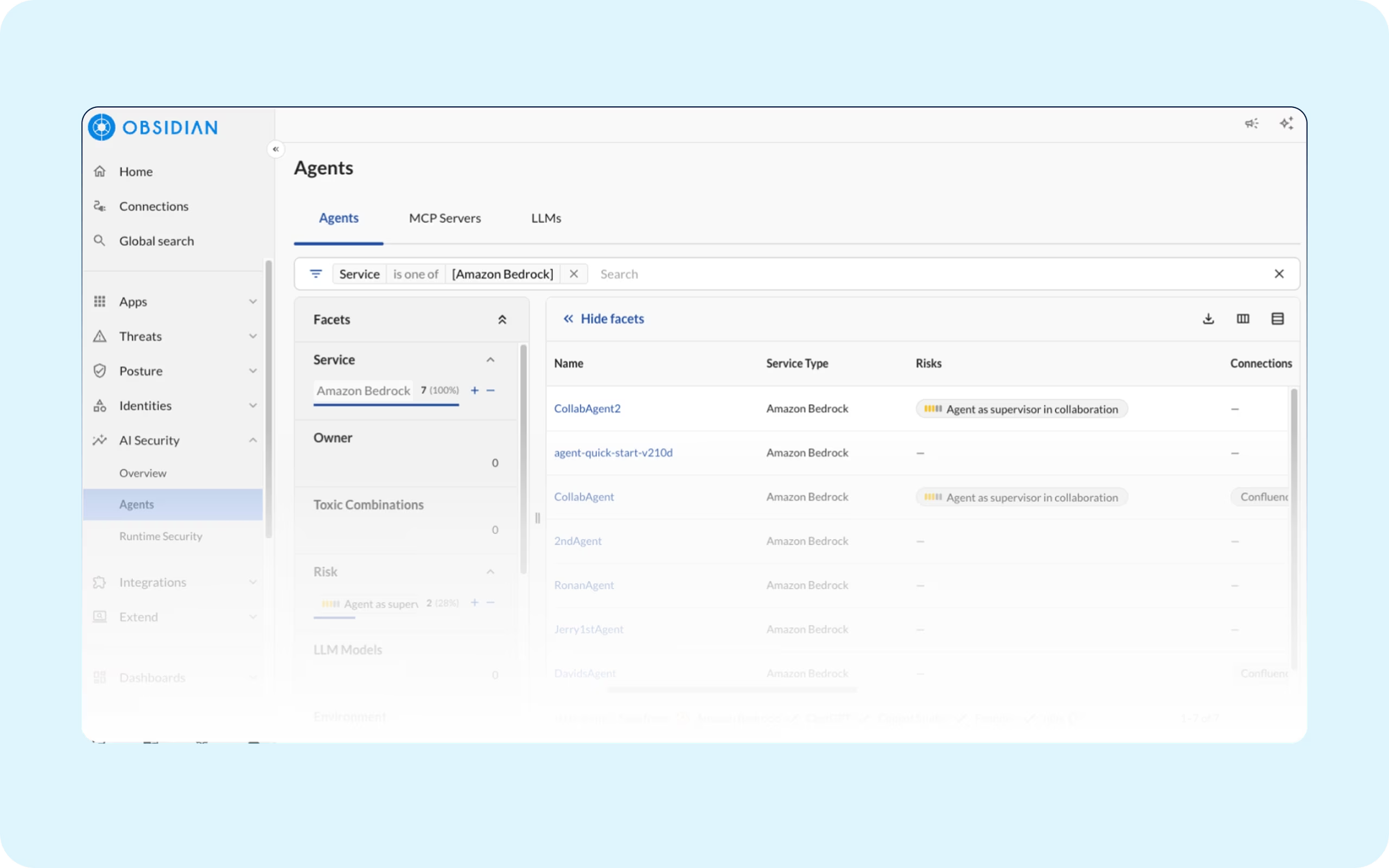
No single view of which agents, MCP servers, and models are running across your tenants.
Native logs weren't built to capture risky tool calls and cross-service actions, especially from agents running outside Bedrock on platforms like Claude.
Agent permissions are scattered across every app they touch. Without a unified view, you can't know your true exposure until something goes wrong.
Agents act on behalf of users but aren't always bound by the same limits. Without a full identity graph, you won't know when an agent quietly exceeds the access its user was granted.
Map, monitor, and manage your agents with a single governance layer.